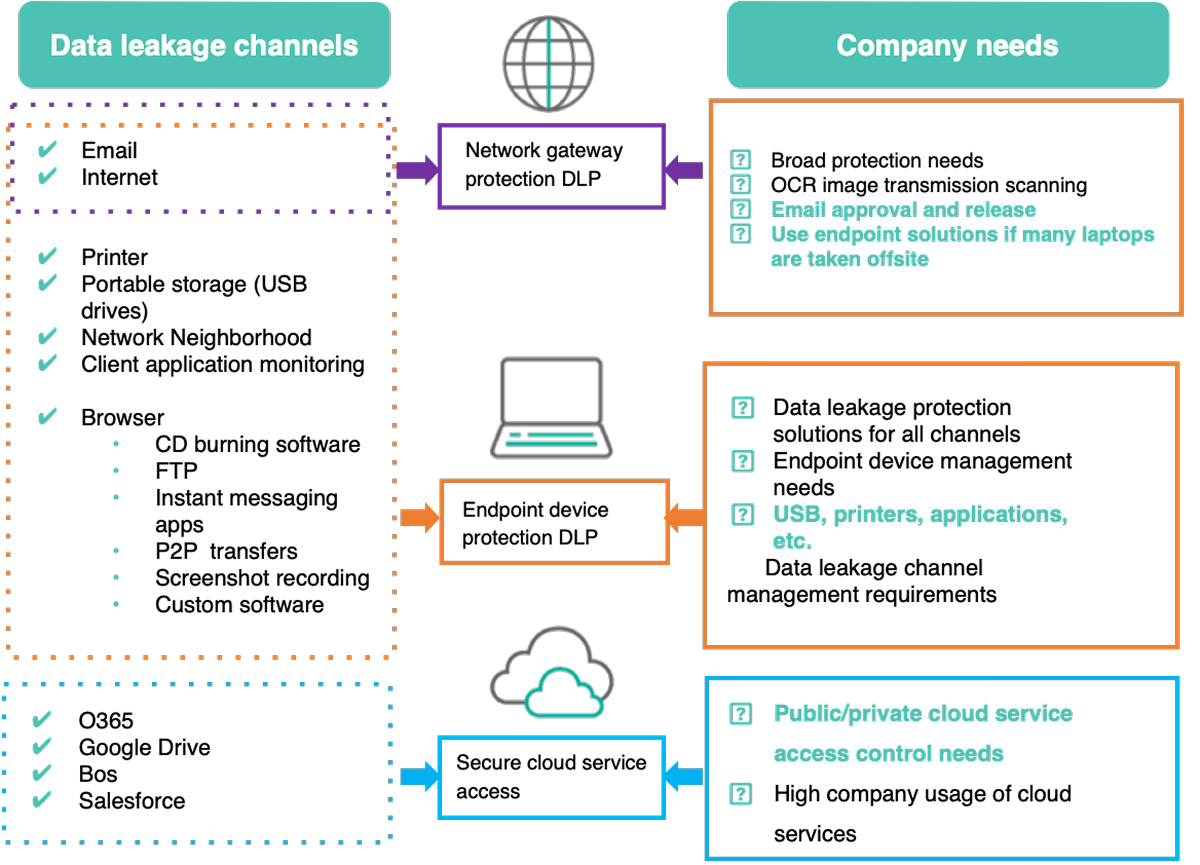
Implementation Opportunities & Preventive Mechanisms
ForcePoint Solution Considerations and Policy Recommendations
DLPP Feature Comparison (Gateway vs. Endpoint)
| Function Comparison | Gateway | Endpoint |
|---|---|---|
| 1. HTTP Leakage Prevention | O | O |
| 2. HTTPS Leakage Prevention | SSL decryption (Forcepoint proxy) | O |
| 3. SMTP Leakage Prevention | O | O |
| 5. Offline User Leakage Prevention | X | O |
| 6. USB Device Leakage Prevention | X | O |
| 7. Burners Leakage Prevention | X | O |
| 8. 5G Connection Leakage Prevention | X | O |
| 9. Printers Leakage Prevention | X | O |
| 10. Architecture | Web: Sniffer model / Proxy model Mail: MTA model |
Agent implant |
| 11. Illegal Mail Review and Pass Function | O (Forcepoint Special features) | X |
| 12. Web Uploaded image OCR recognition | O (Forcepoint Special features) | X |
| 13. Outgoing email image attachment OCR recognition | O (Forcepoint Special features) | X |
| 14. Drip detection, low-rate, multiple-breach detection | O (Forcepoint Special features) | O |
| 15. Integrate with third-party email encryption systems | O | X |
| 16. Automatic copy encryption for external USB drives | X | O (Forcepoint Special features) |
| 17. Keyword Match protection | O | O |
| 18. Filetype Match protection | O | O |
| 19. Policy template match protection | O | O |
| 20. File Fingerprint match protection | O | O |
| 21. Database Fingerprint match protection | O | O |




